Vyatta Web Proxy Setup
So I am currently migrating our office away from the current proxy (Squid running in Windows on our Mail server.I did not set it up.) to a new one, Squid running on Vyatta. So far I have everything setup and working perfectly, however im having trouble getting it to use two different DNS servers, one for internet (8.8.8.8) and another for internal domain name sites. If I set our internal DNS ip first with: set system name-server 192.168.47.1 set system name-server 8.8.8.8 Then it does seem to resolve everything, however any public websites on the internet take an incredibly long time to resolve.
However, if I switch it around so the public DNS is first, websites load incredibly quick but it will only load records in the public DNS. Using nslookup with either setting only seems to use the first name server. Anyone dealt with this before? What is happening with the squid config above is that it's trying to resolve public DNS via your internal server, then waiting for it to fail, then trying public DNS. I would suggest running a separate DNS proxy on the system and tell squid to use that.
Free Web Proxy
Something nice and easy like dnsmasq allows you to set different DNS servers for internal domains, but everything else goes to public internet DNS. Looks like Vyatta includes dnsmasq. Alternatively, set up forwarding on whatever your internal DNS server is to allow it to resolve internet domain names, then just use the one DNS server in squid.
Another Vyatta config guide. And Proxy services. Additionally, an internal web server is published via HTTPS. Configure web publishing.

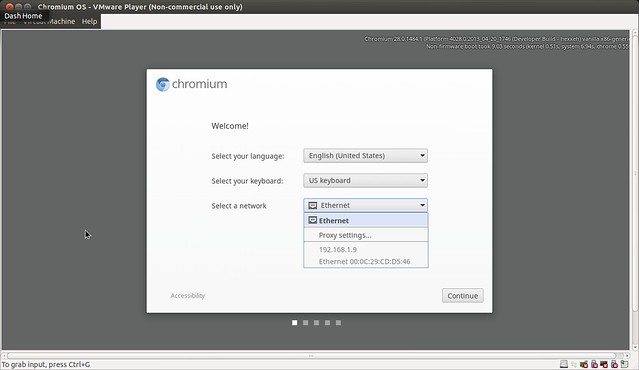
I find myself using the Vyatta virtual router for most everytime I need a router. It hasn't yet replaced my core enterprise routers, but it fits in nicely for smaller environments. This example is going to be a basic home configuration - The internet facing interface receives its address via DHCP, the internal interface is static at 10.0.0.1/24 and provides DHCP, DNS, and Proxy services. Additionally, an internal web server is published via HTTPS. NOTE: I am using Vyatta version 6.4 which changed some of the configuration commands. Confirm the version you are running to ensure the commands are appropriate. Since our external interface will be receiving its IP address from our ISP, we configure it to use DHCP.
To configure eth0 for DHCP, simply type set interfaces ethernet eth0 address dhcp Configure Static Address Our internal network is owned/managed by us, so we can choose to use a private addressing scheme for our systems. To configure eth1 for a static address, simply type set interfaces ethernet eth1 address 10.0.0.1/24 Commit the Changes Whenever you make a change the the Vyatta configuration, it doesn't take effect until you commit them. Additionally, the changes aren't resilient (don't remain after reboot) until you save them. To commit the changes, type commit To save the changes, type save 3. Configure the services System Names We want to give our router a descriptive name as well as create an internal domain name.
In this case I am naming it intRtr for internet router, and giving it a domain of goad.local. This gives me a unique name and domain to identify the router and other systems. Set system host-name intRtr set system domain-name goad.local DHCP Next we configure the DHCP server on the router. This involves creating a pool of addresses for DHCP to use, configuring the default gateway, DNS server and domain name. Set service dhcp-server shared-network-name ETH1POOL subnet 10.0.0.0/24 start 10.0.0.65 stop 10.0.0.199 set service dhcp-server shared-network-name ETH1POOL subnet 10.0.0.0/24 default-router 10.0.0.1 set service dhcp-server shared-network-name ETH1POOL subnet 10.0.0.0/24 dns-server 10.0.0.1 set service dhcp-server shared-network-name ETH1POOL subnet 10.0.0.0/24 domain-name goad.local set service dhcp-server shared-network-name ETH1POOL authoritative enable. PROXY Now we set the outbound proxy set service webproxy listen-address 10.0.0.1 set service webproxy listen-address 10.0.0.1 disable-transparent NOTE: This means that clients will have to configure their browsers as to utilize the proxy 4. Configure outbound NAT for all traffic For anything other that web traffic (or web traffic we don't want to proxy), we enable Network Address Translation.
Set nat source rule 10 source address 10.0.0.0/24 set nat source rule 10 outbound-interface eth0 set nat source rule 10 translation address masquerade 5. Ms-9600 manual. Configure web publishing Finally, we want to publish the web server so that when someone browses to port 443 on the external interface, it is forwarded internally.